CISOs are battling for the right insights to make decisions, the right amount of budget and resourcing, and the right seat at the table. It’s time to take control and ownership over cyber risk management.
In today’s business environment, companies are often focused on how to best use technology to acquire new customers and improve the customer experience, as these IT applications help generate revenue for the organizations. But every CISO knows the more IT infrastructure connected to a system, the larger the organization’s attack surface is—which translates to more cyber risk.
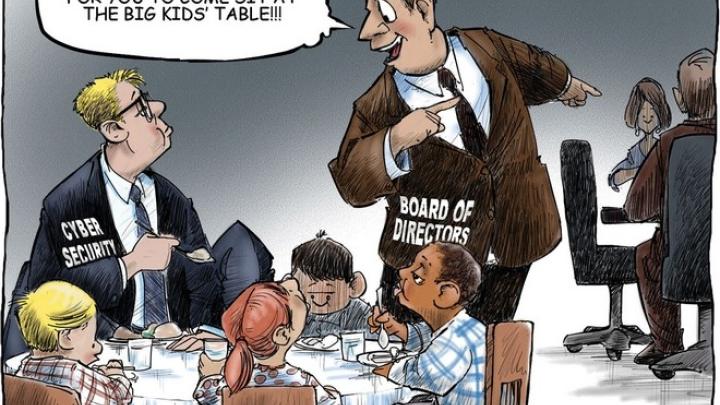
Because of these security concerns, some CISOs bottleneck the technology integration process, forcing other departments to work around them and keep them out of business technology decisions.
But the chief information security officer’s roles and responsibilities have modernized, and it’s widely understood that the more traditional way CISOs might think is now inadequate. Below, we’ll walk through four insider tips on how you (or your CISO) can help your organization grow and succeed while still focusing on security.
4 Insider Secrets Of The Superstar CISO
1. Think of security as a differentiator instead of a cost center.
Those who think of security as a cost center are primarily focused on spending (and protecting) their budget, but aren’t nearly as interested in improving cybersecurity metrics.
But these CISOs are missing an opportunity to turn security into a differentiator. In other words, the role of the chief information security officer should include demonstrating a solid security posture to potential clients or customers to win business. Someone who thinks this way will focus on how security strategies can be used to improve your competitive positioning in addition to protecting the business.
2. Focus on risk management, not compliance.
Regulations compliance is tactical — and necessary — but risk management is strategic. If you’re focused on directing all resources toward compliance instead of lowering your organization’s risk, you’re missing an opportunity to become more tied into the business. Today’s CISO needs to understand how their security recommendations affect the business as a whole.
The Evolution of the CISO
The Evolution of the CISO
3. Look toward fast, automated cybersecurity solutions instead of slow, manual methods.
Consider third-party cyber risk: Old methods of managing it include questionnaires, on-site assessments, penetration tests, and more. In the meantime, business units around you are waiting—usually impatiently.
The modern CISO understands the criticality of incorporating automation and technology to speed up and strengthen their third-party cybersecurity process. For example, Bitsight Security Ratings enable you to get real-time updates on every vendor’s cybersecurity posture. If the status changes (for better or worse), you’ll know right away—and can quickly put the right controls in place to protect your organization and its data.
4. Emphasize collaboration over isolation.
There’s a big difference between CISOs who believe people should follow their advice blindly, and those who inspire numerous security champions throughout the organization. When you collaborate with colleagues in other business units, fewer people will try to bypass you when it comes to business decisions—thus creating less risk for your organization.
Today’s CISO needs to create enterprise value, not burden the organization with obstacles. If you’re not being responsive to business needs, the business will find a way to work around you. Instead of finding reasons to stop progress in its tracks, focus on forward progression.