
Special thanks to Venky Ganesan, the managing director of Menlo Ventures, for his insights into this topic.
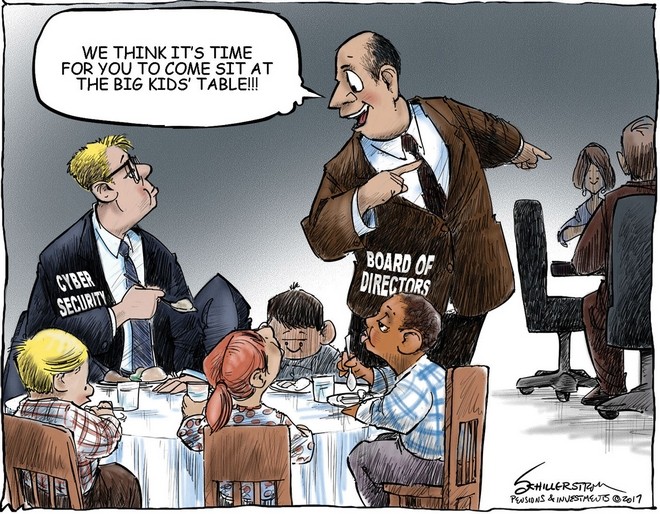 Cybersecurity training for boards of directors has become more common in recent years. But just because cybersecurity in general is being more widely discussed, that doesn’t mean the right information is always being passed along.
Cybersecurity training for boards of directors has become more common in recent years. But just because cybersecurity in general is being more widely discussed, that doesn’t mean the right information is always being passed along.
Your board doesn’t need….
- A tremendous level of technical detail on your cybersecurity program. For instance, the type of security architecture you’re using isn’t of the utmost importance during a board presentation.
- Multiple individuals in charge of reporting cybersecurity. Instead, appoint one person to consistently report to the board.
- Overstated cybersecurity risk. Consistently exaggerating the level of risk your organization is facing won’t help you in the long run.
Boards need more information about cybersecurity than ever before—and this ebook can help you present it effectively.
Whether you’re a CISO or someone else who is tasked with reporting cybersecurity to the board, how do you determine exactly what they need to know? The four things below will get you started.
4 Things To Emphasize In Your Cybersecurity Presentation To The Board Of Directors
1. Cybersecurity is like any other risk situation.
Your board must understand that cybersecurity risk should be treated like any other kind of organizational risk: operational, financial, legal, etc. Boards are less likely to feel comfortable with the subject matter as opposed to, say, financial risk, but cybersecurity requires the same level of emphasis.
2. Cybersecurity is about risk mitigation, not risk removal.
Now that your board knows they’re taking on a risk situation, they need to know your proposed strategies to mitigate that risk. Note the use of the word mitigation, not removal. As Venky Ganesan, managing director of Menlo Ventures, puts it, “You can’t avoid hurricanes. But you can know a hurricane is going to happen and have a clear idea of what to do when it hits.”
3. Your proposed risk mitigation strategy.
While your board doesn’t need to know technical details, it does need conceptual understanding of the overall mitigation strategy. For example:
- What policies and procedures are in place if a breach takes place?
- Who gets notified in the event of a breach?
- How does an event get escalated?
- What insurance policy do we have in place?
- How will our continuous monitoring platform help us?
- What remediation techniques are in place post-breach?
4. What other organizations have gone through with regard to cybersecurity.
To help board members truly appreciate the criticality of cybersecurity, highlight the experience of other companies. “Cybersecurity can be a very abstract concept,” explains Ganesan. “What is not abstract is knowing what has happened to other companies in case of a breach, and the consequences of that breach.” Consider the 2013 Target breach, in which many of Target’s board members were sued and an oversight committee recommended replacing the board.
Additionally, you may want to highlight any regulatory pressures in your business or industry relating to cybersecurity and how to address those appropriately.
Hit all the high notes in your next cybersecurity board report.
It’s one thing to keep these four elements in mind regarding cybersecurity risk and the board of directors—but it’s another to make sure that presentation is compelling. Are you prepared? You will be in no time with this guide.
It will help you nail down your presentation goals and style, and determine which metrics your board will care about the most; it also offers a number of helpful presentation tips. Download the guide for free below!