Read about the latest cybersecurity news and get advice on third-party vendor risk management, reporting cybersecurity to the Board, managing cyber risks, benchmarking security performance, and more.
Insights blog.
Read about the latest cybersecurity news and get advice on third-party vendor risk management, reporting cybersecurity to the Board, managing cyber risks, benchmarking security performance, and more.
Slicing through CISA’s KEV Catalog

Slicing through CISA’s KEV Catalog
Dive into the critical insights of CISA's Known Exploited Vulnerabilities (KEV) Catalog with Bitsight’s latest blog! Discover how KEVs, which signal urgent cybersecurity risks, are being tracked and mitigated across industries. Learn why addressing these vulnerabilities quickly is vital and how it impacts organizational security.

As the world adjusts to more working from home, IT teams worked overtime to enable remote access for millions of employees.

To be effective as a security leader you must find ways to help your SOC teams improve cyber vulnerability awareness and time to remediate. Let’s explore how.

Learn how to scale your cybersecurity program with automation, continuous monitoring, and powerful data insights.

How cybersecurity leaders can manage an expanding attack surface, increasing vulnerabilities, and growing demands from stakeholders.

Imagine you've alerted your IT team to a critical infrastructure error plaguing your network. You ask them to drop their current work and focus on immediate remediation of this detected vulnerability. After further investigation, however, it is found to be a false positive.
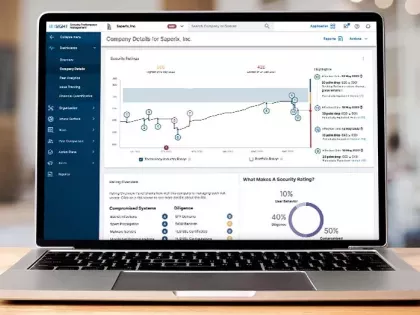
Security ratings, or cyber security ratings, are a data-driven, objective and dynamic measurement of an organization’s security performance. Thousands of organizations around the world use Bitsight Security Ratings as a tool to address a variety of critical, interconnected internal and external use cases at scale in order to enable more effective decision making throughout the global business ecosystem.

As the attack surface expands, vulnerability management offers a strategic approach to manage exposure and remediate on time. Here's what you need to know.

The recent rise in ransomware attacks and business-halting data breaches has made it clear that your organization must prioritize cyber security performance. But ad hoc security controls and defensive measures are not the answer. Instead, you need a strategic, risk-based approach with a cyber security road map as your guide.

Learn what three key metrics can help you create a cybersecurity board report that tells a good story and resonates with your board.

The cybersecurity controls used to manage an organization’s cybersecurity program in previous years will not work against bad actors targeting networks today. Organizations rely more on cloud computing technology, connecting their sensitive data to more third party networks and in turn expanding their attack surface.

A study reveals the correlation between these security flaws and the likelihood of cybersecurity incidents. Learn more.

Learn how to measure the financial impact of cyber attacks so you can have meaningful conversations with business leaders about risk management.

Making the best cybersecurity decisions starts with a strong foundation of data and utilizing advanced analytics to track security performance.

Bitsight enables companies to create a rating based on the infrastructure that best represents their company, called a Self-Published rating, and then share it publicly as a Primary Rating

Your interconnected supply chain needs trust in you, and you in them. But how can you build trust when visibility is low and resources are limited?