Read about the latest cybersecurity news and get advice on third-party vendor risk management, reporting cybersecurity to the Board, managing cyber risks, benchmarking security performance, and more.
Insights blog.
Read about the latest cybersecurity news and get advice on third-party vendor risk management, reporting cybersecurity to the Board, managing cyber risks, benchmarking security performance, and more.
Bitsight and Google collaborate to reveal global cybersecurity performance

Bitsight and Google collaborate to reveal global cybersecurity performance
This joint study between Bitsight and Google arms organizations with actionable insights, providing the current status of global cybersecurity performance by analyzing nearly 100,000 global organizations across 16 cybersecurity controls and nine industries amid heightened stakeholder demands on cybersecurity strategy.

While your current Vendor Risk Management (VRM) or Third-Party Risk Management (TPRM) program may have areas of strength, there is most certainly room for improvement. These programs are a significant driver of both internal and external advisor time, extremely costly, and limited in scale. How can you harness more actionable insight to scale your program and truly and continuously understand the cybersecurity of your third parties? Using Bitsight Security Ratings, you can see a positive impact on your TPRM/VRM program by getting more value out of what you are already doing.

Bitsight is thrilled to announce Bitsight Sovereign Security Ratings, the first objective measurement of national cybersecurity performance. Sovereign Security Ratings measure the security hygiene of nations by observing their IP space and collecting externally observable data on the presence of machine compromise and malware, security diligence, and user behaviors. Government agencies and Computer Emergency Response Teams (CERTs) can use Sovereign Security Ratings to measure, monitor, compare, and investigate the cybersecurity risk of their country and the companies that are critical to its infrastructure.

Security Ratings are still a relatively new phenomenon. As a result, many security and risk professionals are still familiarizing themselves with how ratings work, the data used to compute ratings, and how ratings are put into action. We expect this education to continue: consumer credit scores are always changing and after many years, people are still constantly coming up to speed with the multitude of factors that affect their score.
Since our foundation in 2011 as the first company to provide a rating for measuring a company’s cyber security, Bitsight has become the world-leading security ratings provider. Bitsight is used around the world by industry leaders, country governance systems, as well as smaller organizations alike to take control of their cyber footprint, using safe and objective rating techniques. What does Bitsight do to stand apart from others in the security industry?

Bitsight is proud to announce the release of new features that provide expanded data breadth to all customers. These new innovations enable customers to better identify risks in third party networks and their own networks. Annotations, a new innovation in the security ratings market that allows customers to add tags to specific parts of their network asset maps, providing context for customers to take appropriate action with new events on their network or the network of a third party. Furthering Bitsight’s mission to provide actionable data, Patching Cadence, the newest Diligence risk vector, is expanding data breadth in the platform. This risk vector evaluates a company’s responsiveness in patching major vulnerabilities. Learn more about these features that are helping customers better manage and streamline their security risk management efforts:

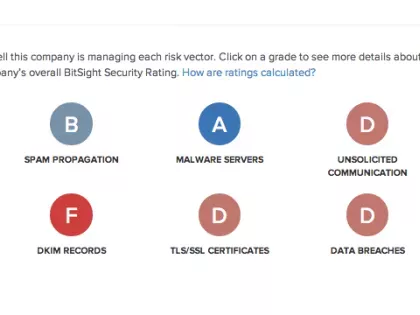
Bitsight has grown tremendously over the last few years, and we’ve learned a lot about the many ways our customers are using Bitsight Security Ratings. With over 400 customers (including 42 Fortune 500 companies) and 2,000 users from diverse industry sectors, companies from around the globe are now using Bitsight Security Ratings to gain insight into their security performance. Moreover, companies are using their ratings to identify and mitigate third party risk in addition to any immediate threats emerging on their own networks. Here’s a look at how Bitsight has been adopted at organizations across a few industries.

In today’s cyber threat landscape, organizations must know how secure they are at any given time. One of the most important questions that security professionals and risk managers can ask is “how secure am I right now?”

In the majority of organizations, vendor risk management is still a highly manual process, making risk assessments a labor intensive exercise for all parties that are involved. This is why, at best, most vendor management programs only assess third parties on an annual basis or during contract negotiation. However, risk managers know from securing their own networks that annual assessments tell us little about how effectively they are responding to emerging threats or addressing new vulnerabilities. So, how are annual vendor risk assessments making us more secure?

I received the following questions from an inquisitive undergraduate student eager to learn more about Bitsight and security ratings. He posed excellent and insightful questions, and I thought that I would share our exchange in case others might be wanting to ask the same questions. Thanks, Nick!

The last few weeks have been a whirlwind of activities here at Bitsight! Between attending and speaking at RSA, participating in the latest Verizon DBIR report, preparing for our session at FS-ISAC, announcing our new partnership with AIG, and being featured as a vendor risk management solution in the Wall Street Journal, we were happy to see the second quarter off to such an exciting start. And then we got even more good news!

The idea of telling a vendor or potential vendor that you've rated their security performance can be a little daunting. If someone has never heard of a Bitsight Security Rating, being told that another company has been monitoring their security effectiveness, without them knowing, can sound a little "big brother-ish" and raise lots of questions about privacy and legality. Though our methods are unobtrusive and based on the same outside-in model of credit ratings, we provide many materials to our customers to help them deal with these types of situations.
During last month's FS-ISAC webinar, Home Depot, the SEC and Increasing Board Oversight: Why Metrics Matter More and More, Bitsight CTO and Co-Founder Stephen Boyer answered questions from attendees about why using IT security metrics is more important than ever before. He also performed a live demo of Bitsight Security Ratings to show how to prove that security ratings work.

During last month's SANS webinar, Quantifying Security Performance: The What, Why and How of Security Ratings, Bitsight CTO and Co-Founder Stephen Boyer answered questions from attendees. Here are some of the most interesting questions people posed, and our answers for each one. There are also two clips from the webinar recording.
Bitsight has released new capabilities and features in the Bitsight Security Ratings portal to widen the data breadth offered to customers and give more detailed, granular performance analytics on specific risk vectors. These changes are available to all enterprise, team, and individual tier customers today.
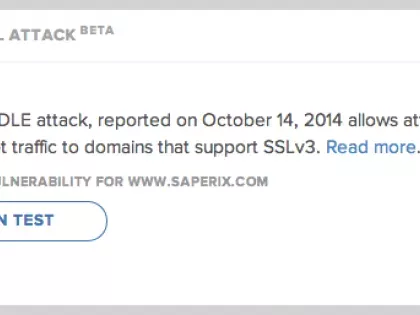
Third party breaches have become a common occurrence in the last year. From Target to Home Depot and Goodwill, major organizations have been compromised from vulnerabilities present in their extended network ecosystems. Compounding fears surrounding third party vulnerabilities, the last year has also seen no less than three major security flaws affecting basic internet protocols. The first two, Heartbleed and Bash, grabbed media headlines and left businesses scrambling to ensure they weren't left vulnerable. Just this week, another major security flaw dubbed Poodle was uncovered by security researchers. This bug affects SSL v3, a widely used protocol to secure communications over the internet. With growing concern about third party security and the seemingly neverending revelations of internet bugs, organizations are left wondering how they can better gain visibility into the vulnerability of their third parties when it comes to basic configuration hygiene.