Bitsight Third-Party Risk Management empowers risk leaders to manage their digital ecosystem from start to finish. Accelerate vendor assessments. Continuously monitor and uncover blind spots across your digital ecosystem. Take action on exposure swiftly and confidently.
Bitsight Third-Party Risk Management empowers risk leaders to manage their digital ecosystem from start to finish. Accelerate vendor assessments. Continuously monitor and uncover blind spots across your digital ecosystem. Take action on exposure swiftly and confidently.
Mitigate risk. Enable the business. Reduce exposure.
Vendor Risk Management
Vendor Risk Management
Scale vendor risk management to enable business growth.
Don’t let risk assessments be a bottleneck. Ensure third-parties are within your organization’s risk tolerance and manage hundreds of vendors as effectively as you manage ten.
- Increase efficiency with a network of over 40,000 vendor profiles
- Accelerate onboarding with automated assessments
- Validate vendor responses with objective data and evidence
More on Bitsight for Vendor Risk Management
Continuous Monitoring
Continuous Monitoring
Continuously monitor vendor security controls.
The problem is visibility. Gain a full view of your third and fourth parties without missing a step, and improve the security posture of your vendor portfolio to instill trust.
- Detect and address ongoing third-party risk
- Remediate easily with supporting data and evidence
- Discover fourth-party product usage automatically
Detection & Response
Detection & Response
Detect and respond to third-party vulnerabilities at scale.
As threats evolve, all eyes are on your digital ecosystem. Bitsight gives you the confidence to handle unforeseen major security events across third and fourth parties.
- Mitigate emerging zero day vulnerabilities at scale
- Improve efficiency and scalability of vendor outreach
- Focus on what matters most with real-time reporting
More on zero-day detection and response
Quickly and confidently ensure new vendors are within your organization’s risk tolerance
Quickly and confidently ensure new vendors are within your organization’s risk tolerance
“We save hundreds of hours annually by using Bitsight. We’ve integrated Bitsight Vendor Risk Management into our onboarding and evaluation process, and it’s helped us identify the actual risk level associated with vendors.”
- Elizabeth Olson Lennon
Director of Vendor Management, Alameda Alliance for Health
Reduce the reassessment burden and manage constantly changing risk throughout the vendor lifecycle
Reduce the reassessment burden and manage constantly changing risk throughout the vendor lifecycle
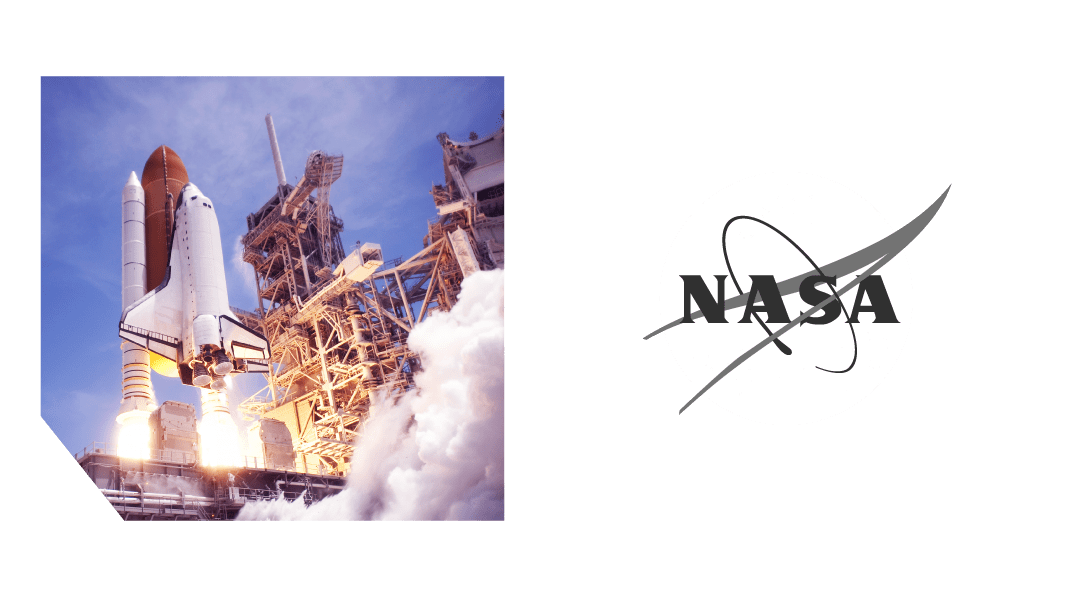
“We can now easily identify the vulnerabilities associated with a particular vendor and how those vulnerabilities could impact our own security posture—before we begin working with them.”
- Kanitra Tyler
ICT Supply Chain Risk Management Service Element Lead, NASA
Deliver credible evidence that your third parties' security controls are being managed effectively
Deliver credible evidence that your third parties' security controls are being managed effectively
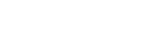
“Bitsight immediately shone a light on hidden risk in our own vendor portfolio, particularly critical third parties in the technology sector.”
- James Arden
Advisory and Assurance Manager, RBC Brewin Dolphin
Resources
Get to know Third-Party Risk Management
End-to-end Third Party Risk Management

End-to-end Third Party Risk Management
5 Keys to Building a Scalable Vendor Risk Management Program

5 Keys to Building a Scalable Vendor Risk Management Program
Bitsight Third-Party Vulnerability Detection & Response

Bitsight Third-Party Vulnerability Detection & Response
What’s Lurking in Your Environment?
What’s Lurking in Your Environment?
5 Proven Strategies to Maximize Supply Chain Cyber Risk Management

5 Proven Strategies to Maximize Supply Chain Cyber Risk Management
Get a Free Look at a Bitsight Third-Party Risk Report

Get a Free Look at a Bitsight Third-Party Risk Report
Download our third-party risk portfolio risk report sample to get an exclusive look at the actionable reporting capabilities third party risk management teams can use to reduce critical portfolio risk.The third-party risk management solution backed by the security rating that started a whole industry.