
When Bitsight pioneered the security ratings market over six years ago, it was the first to use the outside-in approach to security ratings. Although not initially intuitive to many people, the value of this approach has become increasingly clear for many reasons and subsequently, its adoption has become more widespread. At Bitsight, we believe that an outside-in approach is the best way to build a security ratings product, and has proven valuable in many use cases.
Bitsight’s mission is simple: to transform how organizations evaluate risk and security performance using a common, objective, evidence-based, quantitative measurement. This approach Bitsight employs has many similarities to the approach consumer credit agencies have taken to evaluate consumer credit risk. They also collect data independent of the party being rated. In both cases, the party being rated has the right to challenge the data being used to calculate the rating, and the business model stipulates that the party who wants to use the rating pays a fee, as opposed to the party that is being rated.
 While some have questioned if an outside-in approach to security ratings could provide sufficient visibility into an organization’s security posture, most have come to the conclusion that the coverage through this approach is undoubtedly comprehensive. And, what is undeniable, is Bitsight Security Ratings are directly correlated to the likelihood of a company being breached.
While some have questioned if an outside-in approach to security ratings could provide sufficient visibility into an organization’s security posture, most have come to the conclusion that the coverage through this approach is undoubtedly comprehensive. And, what is undeniable, is Bitsight Security Ratings are directly correlated to the likelihood of a company being breached.
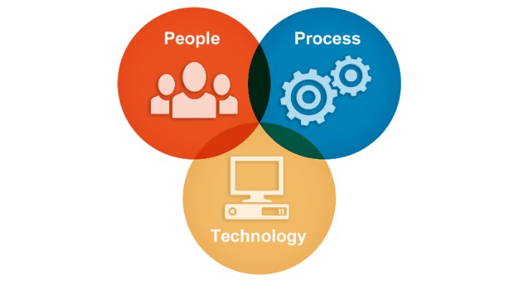
Securing an enterprise, like all other aspects of IT, has three dimensions to it: people, process, and technology. Bitsight’s data is broken down into four buckets that provide coverage across all three of these areas. The data that makes up Bitsight Security Ratings is comprised of 60% compromised systems, 30% diligence information, 10% user behavior, and data breaches (when applicable). Our algorithm takes all of this information and calculates the top level rating on a daily basis. Our algorithm is updated annually to ensure that we are always factoring in the latest risks, given the dynamic nature of cybersecurity. When thinking about measuring security performance and the related risk, it’s critical to think about how technology, people, and process are all functioning together to protect against this exposure. Bitsight’s compromised systems data is primarily evaluating technology, and our diligence and user behavior information are primarily evaluating process and people.
Another way to think about coverage is how much of the technology stack you can observe within the organization, starting at the digital perimeter (firewall), throughout the network, the endpoints, application stack, the data, and the user. Today, Bitsight has more than 20 risk vectors, which look at almost every layer of the technology stack and can evaluate processes and user behavior. Bitsight Security Ratings can also measure the efficacy of people, process, and technology over time. Across these risk vectors, we can examine technology and process breakdowns (or lack of process) as well as see a range of user behaviors that put a company at risk.
In no way is a security rating a sole determinant of the security posture of an organization, but it can and should be a critical part of security and risk decisions. This is just like a credit rating does not solely determine an applicant’s credit worthiness, but is an important part of credit and lending decisions. The fact that Bitsight can see that much of the technology stack consistently across 100,000+ hand-mapped companies spanning the globe gives Bitsight Security Ratings a powerful capability that is almost instantly attainable to help inform and make the analysis of an increasingly critical risk more efficient.