There’s enormous pressure on businesses to get cybersecurity right. Executives are feeling a heightened need to protect their organizations’ reputations and bottom lines. Security managers also feel it as they shield their networks and data from industrious hackers and do their part to protect their businesses daily. In fact, Gartner predicts 40% of boards will have a dedicated cybersecurity committee by 2025.
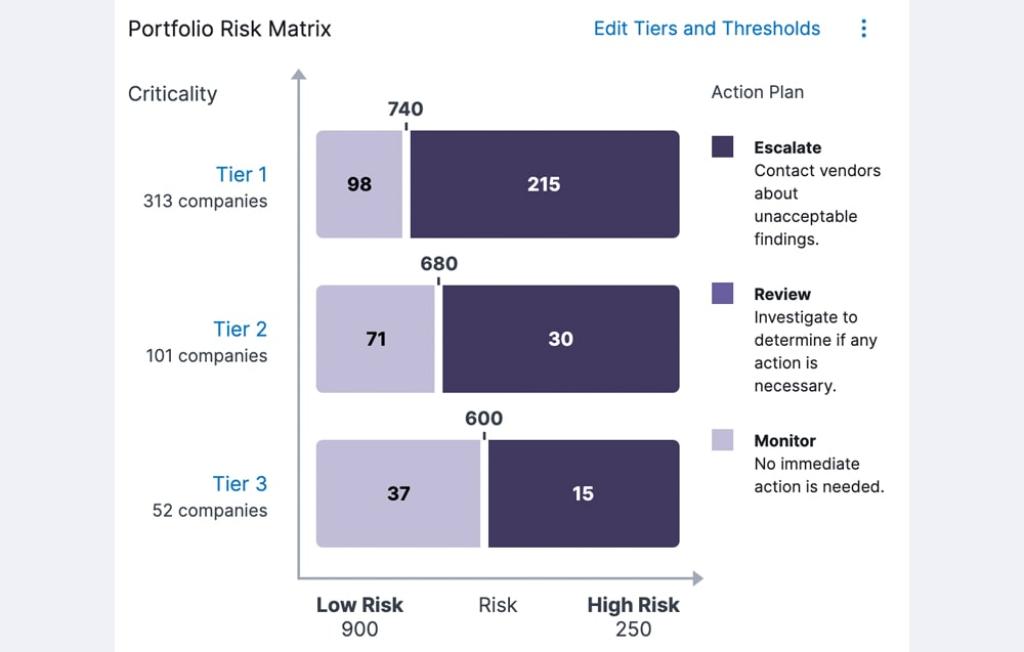
Successful cybersecurity protection can only be achieved if everyone’s on the same page about how best to defend against threats and prioritize budget.
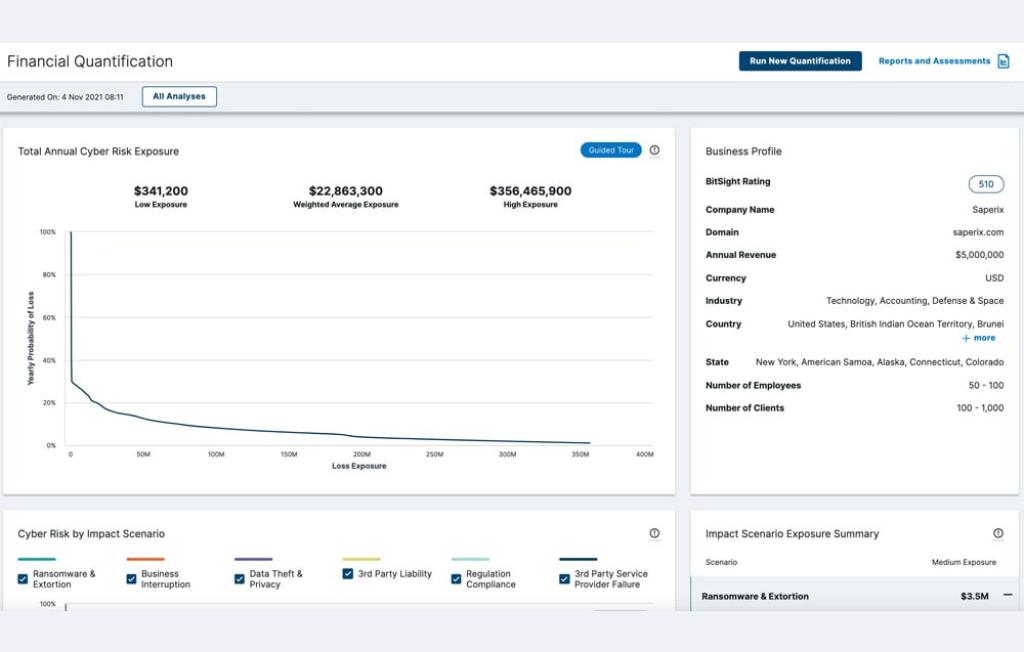
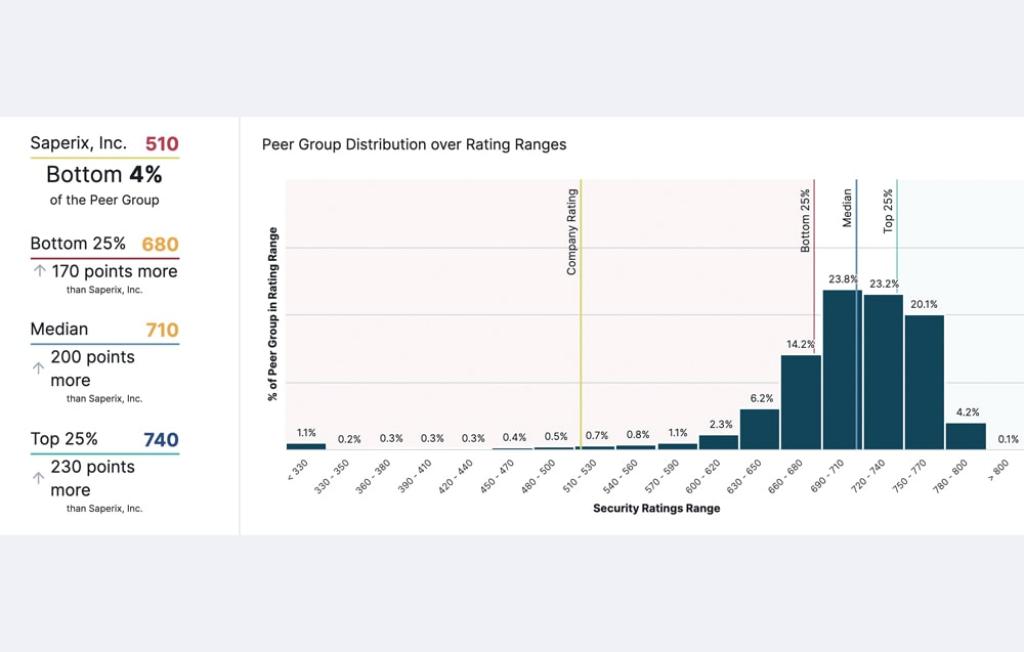
That’s not always the case. Executives aren’t always familiar with technical metrics or jargon, while security managers often aren’t connecting cyber risk to real world business outcomes the C-suite cares about.
Bitsight can help you bridge that communications gap – and better defend against threats.